There is a major misconception looming in the tech world: cyber-crime won’t happen to you. Large companies are not the only targets. Small businesses such as those in the Vail Valley are at risk. We are not in the business of fear mongering, but the statistics are frightening! In a national study published this July, researchers broke down loss in millions of dollars per state. In 2017, Colorado residents and businesses lost 39.94 million dollars to cyber-crime. Global cyber-crime damage costs are projected to hit $6 trillion annually by 2021.
Hackers do not have a specific target in mind when they phish or spoof. Every business, large or small, global or local, should take cybersecuirty seriously. At All Mountain Technologies, we believe educating our neighbors in the Valley is important. We plan on bringing you more education opportunities in the future. The following are ways to improve your cybersecurity and combat hackers!
1. Update Security Tools
Sticker shock aside, the proper hardware and software does wonders for security. We recommend updating the following:
- Business firewall – purpose built UTM device
- Content filtering
- Sandbox email attachments
- Open SSL content
- Intrusion prevention
- Operating system and software updates
- Anti-virus and anti-malware
- Spam filtering
- Maintenance utilities (cleaner, etc.)
- Email encryption and archiving
2. Implement Security Best Practices
Strong passwords are one of the first lines of defense against breaches. Educating staff on changing passwords frequently is a great first step to building best practices. In addition we recommend:
- Password complexity/change policy
- Implement Two Factor Authentication (2FA)
- Never save passwords in your browser
- Create a separate guest wireless
- Use central authentication for all systems
- Review (or develop) permissions for all folders and data repositories
- Encrypt hard drives for laptops
- Ensure phones/tablets can be wiped remotely
- Disable USB ports on all computers
- Do nothing private on a public network
- Maintain (and test) robust backups
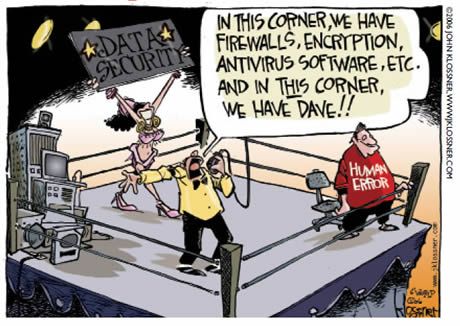
3. Combat Human Error with Employee Education
Create a security aware culture. Establishing a security best practice with your staff will set the stage for success. Continuing to educate your staff on what to look for as new tools become available will decrease chances of phishing and spoofing. Here is Open DNS’ Phising Quiz to test out!
4. Update Regularly
Any connection to the Internet is vulnerable. Keep every connection, operating system, and application up to date with patches and enhancements. Implementing software and system security updates quickly limits possible exposure to vulnerabilities.
5. Establish VPNs for ALL Connections
Networks that are protected only by generic security measures are more vulnerable to attack. Implement virtual private network (VPN) connections between office locations. VPNs are great for remote employees who may connect through public Wi-Fi service as well.
6. Retire Unused Services
Contrary to popular belief, most old computers do not hold their value. We anticipate archaic machines will not be worth thousands of dollars on eBay in the future. When limited-duration products expire, decommission the applications, logins, and user credentials associated with them. In cases when you don’t use every available feature of a UC deployment, such as a video chat function, turn it off to further limit unauthorized access.
7. Back it Up
Backing up data is not only to keep information updated, but also secure. Multiple backups is always recommended. Archiving data that is not needed on a daily basis can help you stay organized and efficient.
8. Don’t Forget Mobile Devices
For remote users mobile devices are crucial. As a business it is your job to make sure your staffs’ mobile devices are equally secure if company information is being shared. Sensitive browsing, such as banking or shopping, should only be done on a device that belongs to you, on a network that you trust. Whether it’s a friend’s phone, a public computer, or a cafe’s free WiFi—your data could be copied or stolen.

9. Monitor, monitor, monitor
Would you set up security cameras and not monitor them? Cybersecurity works the same way. Be sure to monitor your accounts for any suspicious activity. If you see something unfamiliar, it could be a sign that you’ve been compromised.
10. Don’t Leave Devices Unattended
Never leave your devices unattended. If you need to leave your computer, phone, or tablet for any length of time- lock it up so no one can use it while you’re gone. If you keep sensitive information on a flash drive or external hard drive, make sure to lock it up as well.
If you have any questions regarding your business’ cybersecurity or technology support, reach out to Allie Yazel at ayazel@allmtntech.com or visit https://allmtntech.com/.